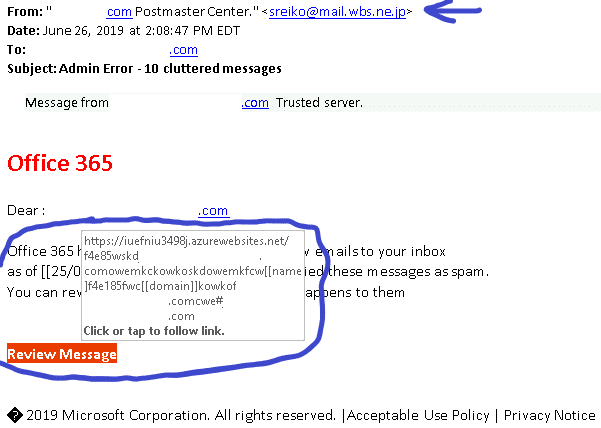
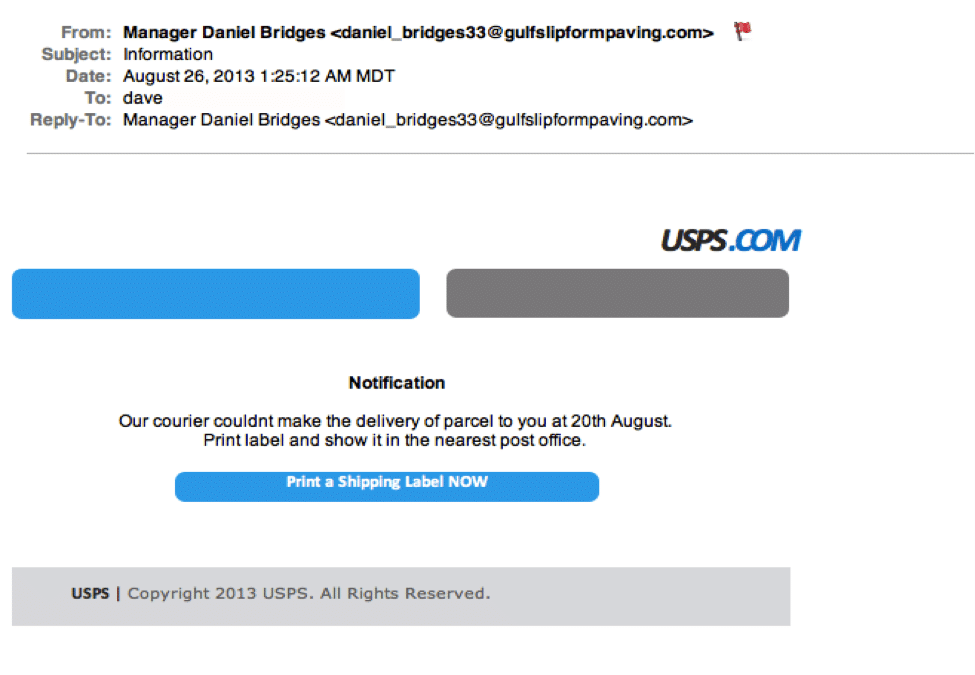
1. Who is it from? The number one easiest way to tell if an email you are reading is a phishing attempt is to read who the email is from. Hover over the email address, expand it out. If you see the email is supposed to be from Bill Murray <[email protected]> but instead it says Bill Murray <bill@murraayy.com>. That is without a doubt a phishing email. On top of that if you see a reply-to field, ensure that matches with what it should be as well.
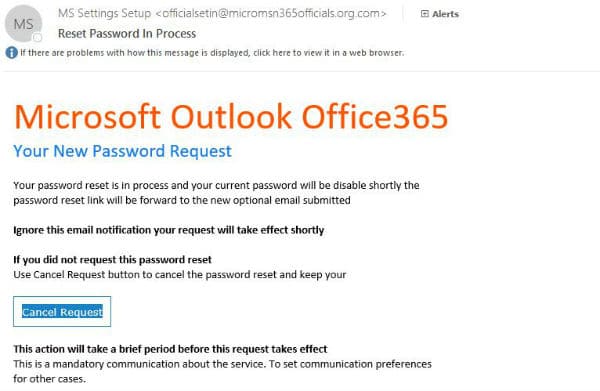
2. Check your links. Before you click on any links in the email, hover over them. If the website matches up with the intention of the email then you’re fine. However let’s say you were sent a password reset form for office 365, a common email platform among business users. The email has a link directing you to a password reset page. When hovering over the link it says https://www.mycrosawft.com/passwordreset instead of https://www.microsoft.com/passwordreset. Check the domain (whatever.com) to determine how safe that link is.
3. Intention of the email. Let’s say you received a password reset email pertaining to Office 365. Think about it for a second. Did you request to reset your own password? No? Obvious phishing attempt.
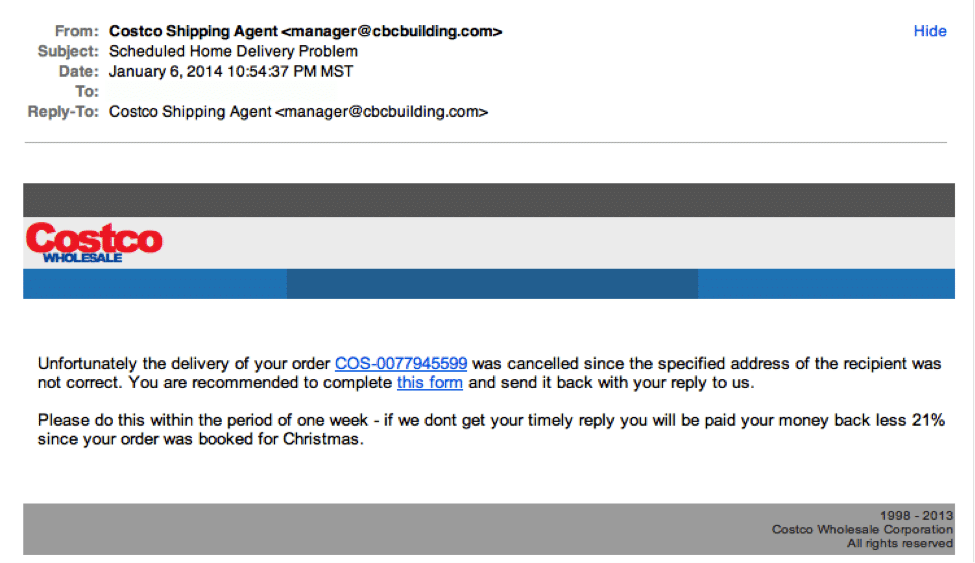
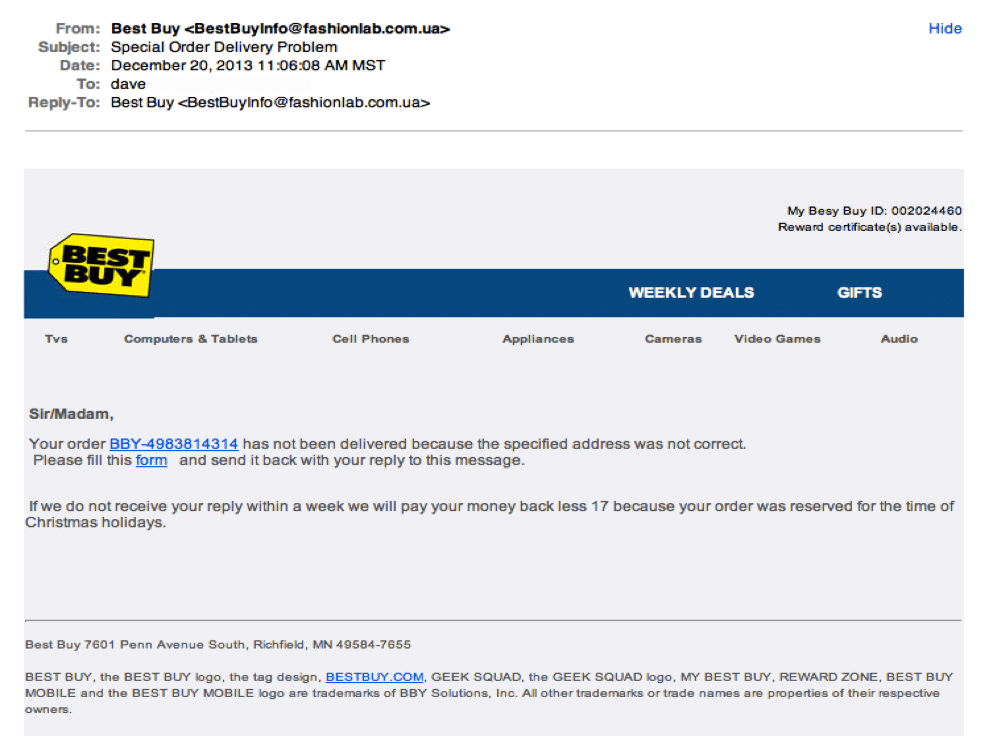
Let’s say you received an email pertaining to a item being shipped to your home. Did you order anything from anywhere online? No? Obvious phishing attempt.
A majority of hacking consists of social engineering. If they can convince you that you need to click that link and input the data they want, then they have already won.
Think about the email before you act on it.
4. Grammar. A lot of attackers are foreign. English is their second, third, or fourth language. This is usually evident in the amount of spelling mistakes that can be found within the email. Possibly even the difference in spelling of a word (Example: color vs colour).
5. Companies don’t force you to their website. Some phishing emails come as a giant image looking like a regular email. You click anywhere on that image and it will take you to the site that phishes for information they want.
Ensure You And Your Employees Are Protected Today
All it takes is one employee not knowing these simple rules to click the wrong link and allow hackers into your systems. It is common these days that once a hacker has gained control of one computer, they can control the rest. This is why you partner with a proper IT company such as IPM Computers to manage your systems and ensure that proper permissions are managed and proper securities are in place. A proper IT company will also maintain encrypted off-site backups of all of your files as a final fail safe in case a hacker manages to bypass every measure out there.