I just fell for a phishing email.
Yep, the guy who builds services to protect clients from phishing emails was tricked by a phishing email!
Now, I didn’t click on anything or give up confidential information but I did think a phishing email was a real email and forwarded it over to my staff to take a look at. It was embarrassing when my CTO pointed out that this was clearly a phishing email.
Here’s how it happened:
- I was in the middle of dinner (along with a glass of wine) and checked my email on my iPhone (the first mistake was interrupting dinner to check my email but that goes along with the joys of being a CEO).
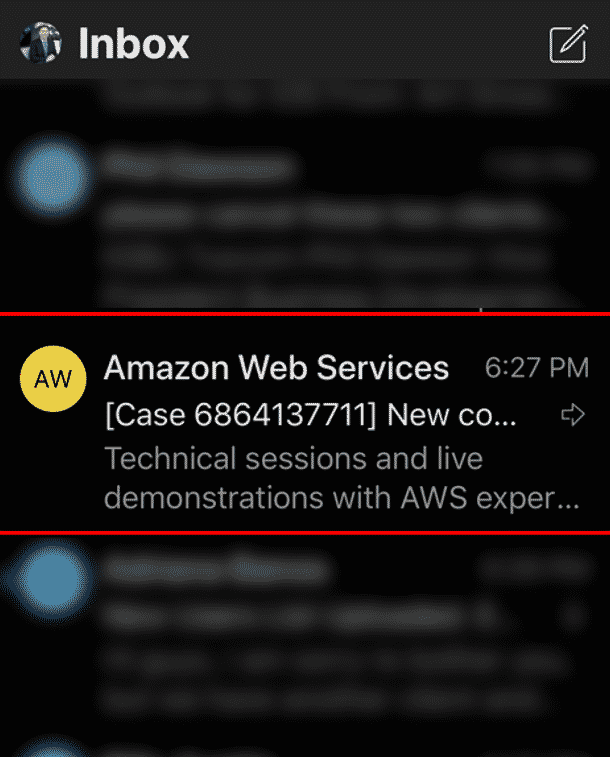
- I wanted to quickly swipe through my email and get back to dinner and conversation with my wife. I saw an email for Amazon Web Services (AWS) – which is our hosting platform for our SasS cybersecurity services.
- It looked like an email from Amazon Web Services and usually, I am copied on these types of emails. This is not out of the ordinary and I just assumed we were working on a technical issue that this email was in reference to. I opened the email.
- I looked at the email and saw that whatever issue we had seemed to be resolved. I couldn’t figure out what the issue was so I forwarded it over to our CTO and Sr. Systems Engineer to take a look at it. I put down my phone, took another sip of wine, and got back to dinner.
- My CTO easily spotted that this was a phishing scam and was nice enough to respond to my email and let me know.
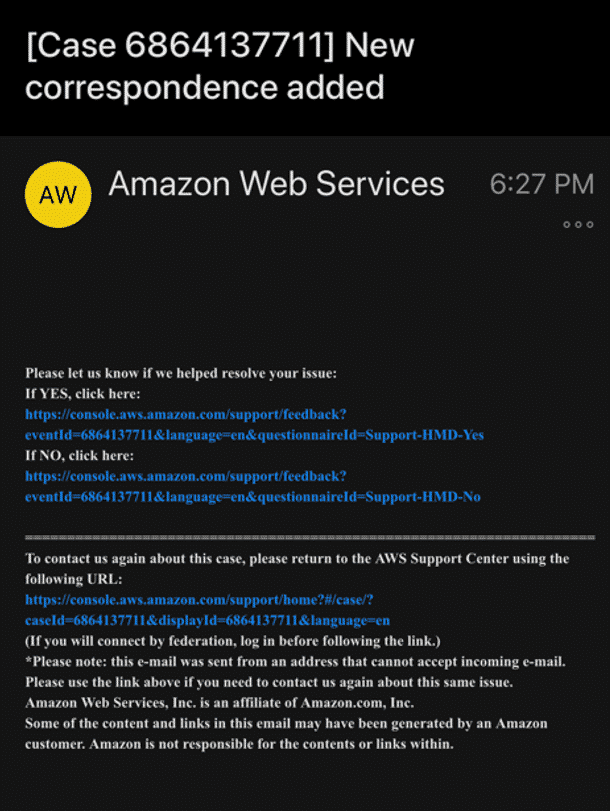
- At that point, I knew that I had fallen for a phishing email because I believed it to be legitimate. Luckily, my CTO spotted the email and didn’t click on any of the links.
- Feeling a little embarrassed I decided to run it through our Catch Phish Outlook Email Analysis Tool . Sure enough, Catch Phish told me that this was clearly a phishing email. 1) The language in the email came back as “Likely” to be a phishing email. 2) The sending domain was different from the rest of the links in the email – a clear sign that this was a phishing email. 3) The country that the email was sent from was Iran, clearly not our US-based AWS services.
- To my defense, on my iPhone, the actual sending email domain was not visible. It appeared to be a legitimate email for Amazon Web Services. We have received many emails from AWS so I was not phased or put on alarm by receiving this email. On my desktop (which I checked afterward), it was much clearer that this email did not come from AWS.
Key takeaways:
- Anyone can be tricked into falling for a phishing email. Given the right time and the right email message, anyone can overlook a phishing email.
- Humans make mistakes (even the guy who posts about phishing all day long). Humans have preconceived notions (in this case – this is an email from AWS, something I believed was probably a support case that I was unaware of).
- Phishing detection tools such as Catch Phish are absolutely needed. Catch Phish didn’t have a preconceived notion. It saw that the domain was spoofed. It saw that the email originated from Iran. It analyzed the language (using artificial intelligence and machine learning) to point out that the email was not legitimate.
In conclusion, I am embarrassed that I was tricked. I am happy that my CTO spotted the phishing email and no harm was done. I could’ve easily swept this under the rug but thought that this was a good story to share. Phishing is really dangerous! Trained employees can fall for scams. Untrained employees stand no chance at spotting fake emails. Automated tools such as Catch Phish are absolutely needed to help spot phishing emails and protect employees.
The post I Fell for a Phishing Scam appeared first on Breach Secure Now!.